Data Masking conceals sensitive information by replacing it with fictional but realistic data, preserving privacy without compromising utility.
It helps protect sensitive data from breaches during development, testing, and analytics.
Data exposure, non-compliance with privacy laws, and increased security vulnerabilities.
With process modeling, RPA bots, regression test scripts, and real-time monitoring, ChainSys ensures end-to-end automation.
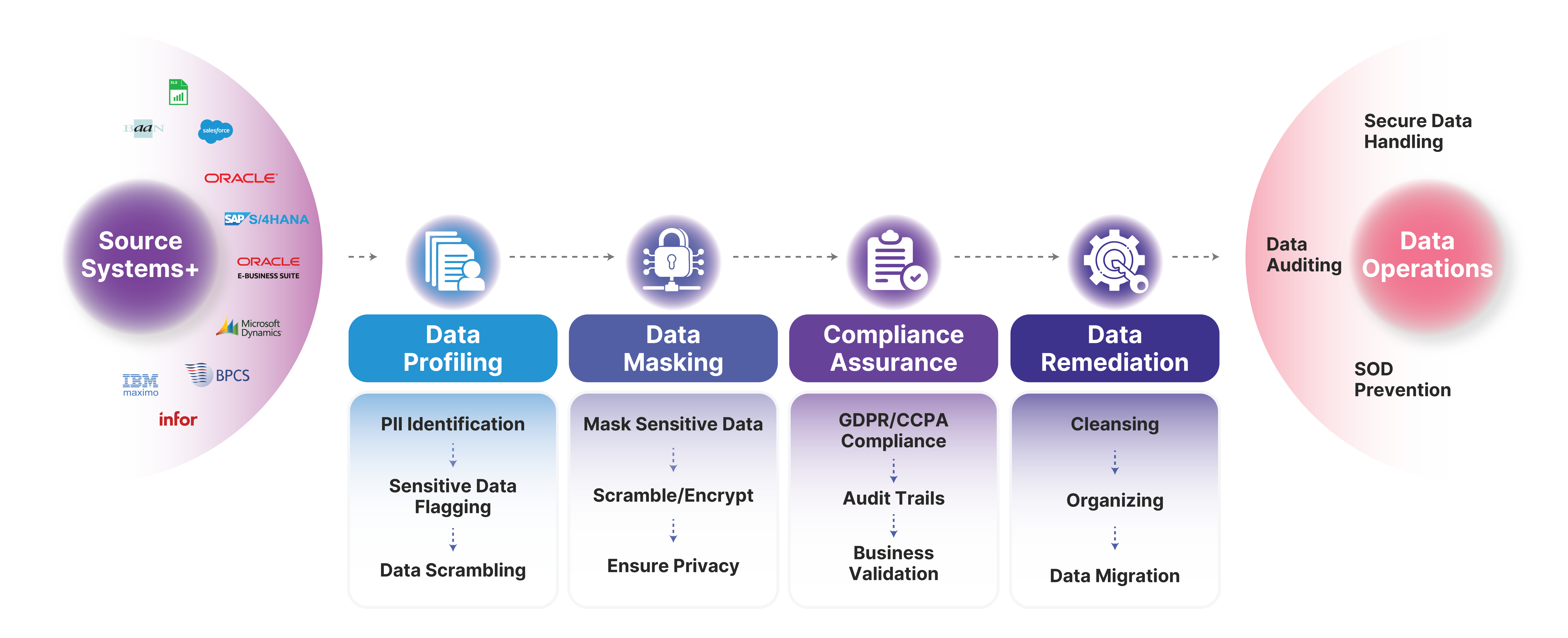
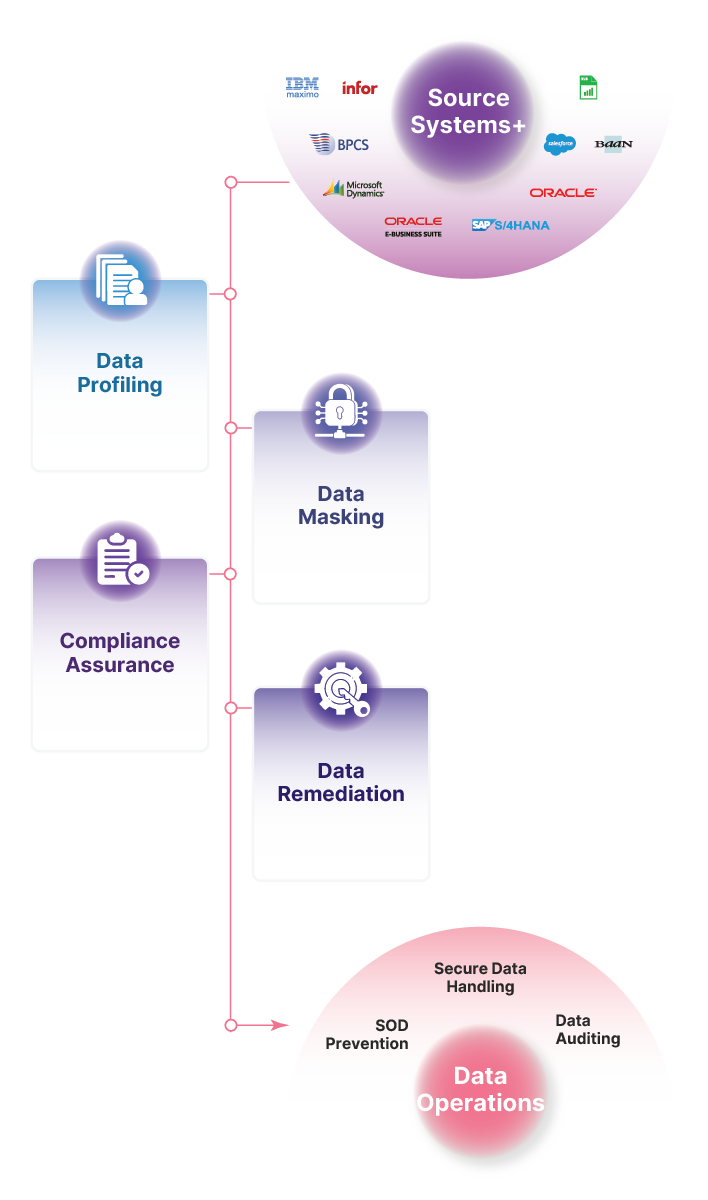

ChainSys's AI-powered platform profiles structured and unstructured data, flagging PII and sensitive data to be masked or encrypted.

The platform provides comprehensive data lineage capabilities, allowing organizations to visualize the entire data journey from source to consumption. This helps in understanding dependencies and identifying potential issues.

By actively using metadata, ChainSys AMM supports automated data quality checks and validation processes. It ensures that data adheres to predefined quality standards before being used in critical operations.

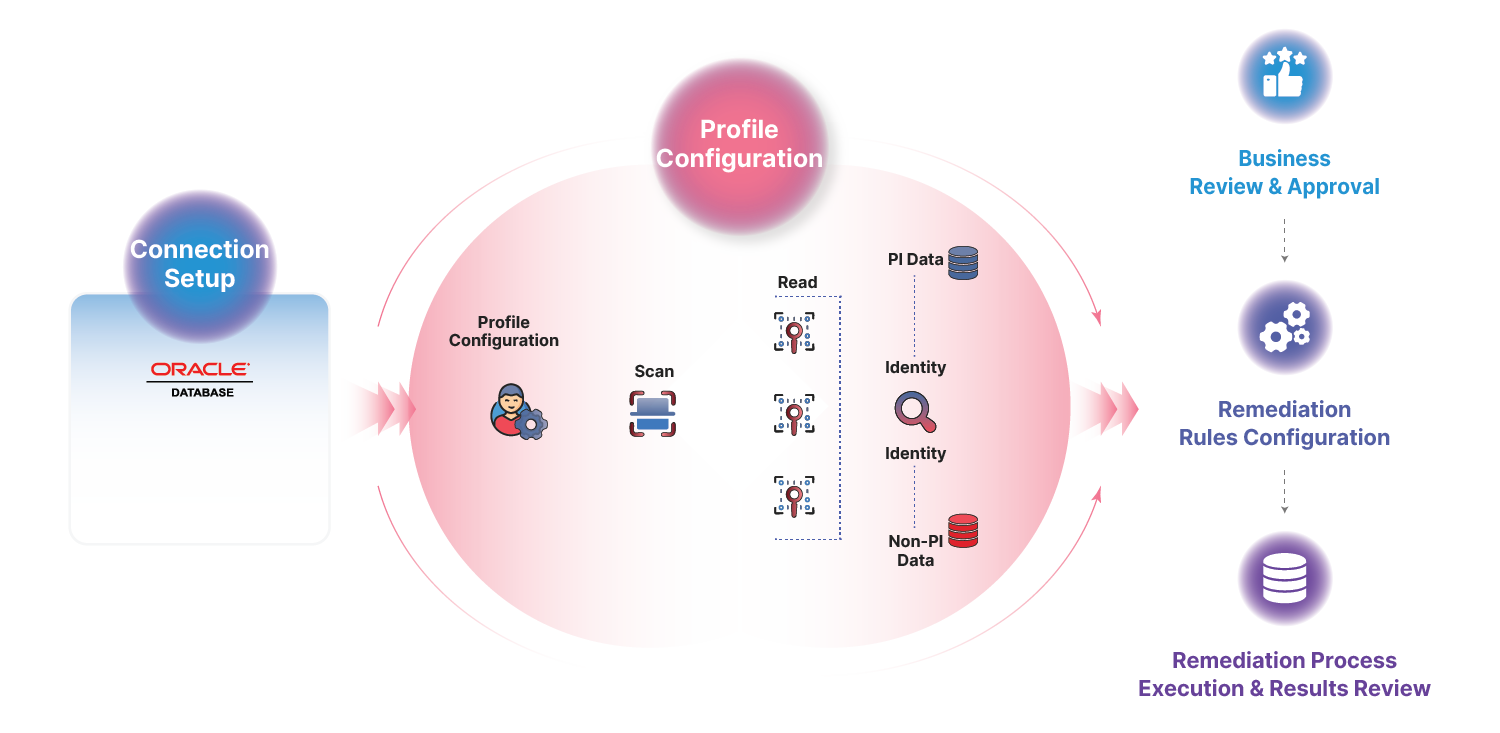
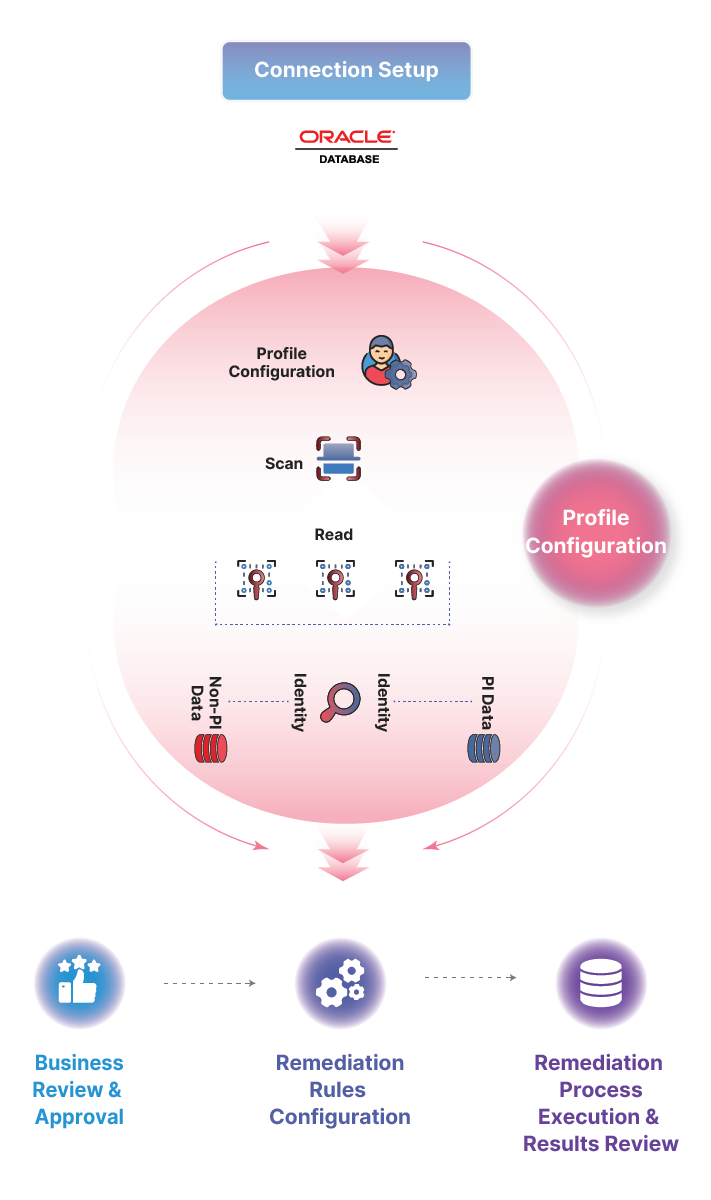
Our meticulous validation process ensures flagged data is reviewed and approved, enhancing the accuracy and reliability of data masking efforts.

ChainSys's AI-powered platform profiles structured and unstructured data, flagging PII and sensitive data to be masked or encrypted.

The platform provides comprehensive data lineage capabilities, allowing organizations to visualize the entire data journey from source to consumption. This helps in understanding dependencies and identifying potential issues.

By actively using metadata, ChainSys AMM supports automated data quality checks and validation processes. It ensures that data adheres to predefined quality standards before being used in critical operations.

Our meticulous validation process ensures flagged data is reviewed and approved, enhancing the accuracy and reliability of data masking efforts.

ChainSys AMM automatically collects and catalogs metadata from various sources, including databases, data warehouses and cloud platforms. This continuous harvesting ensures that metadata is always up-to-date.

The platform provides comprehensive data lineage capabilities, allowing organizations to visualize the entire data journey from source to consumption. This helps in understanding dependencies and identifying potential issues.

By actively using metadata, ChainSys AMM supports automated data quality checks and validation processes. It ensures that data adheres to predefined quality standards before being used in critical operations.

ChainSys’s AMM uses metadata to enforce data governance policies automatically. It includes role-based access controls, policy enforcement, and compliance monitoring, ensuring that data is managed according to organizational rules and regulations.

The AMM seamlessly integrates with enterprise data catalogs, enabling a unified view of all data assets. This integration facilitates better data discovery, tagging, and collaboration across teams.

Tailored migration workflows allow organizations to define specific rules for data mapping, transformation, and validation based on business needs.
Mask confidential data intelligently and stay compliant with ChainSys.
Need to secure test or analytics environments?
ChainSys Data Masking tools ensure that sensitive information, such as Personally Identifiable Information (PII), is securely anonymized, scrambled, or encrypted to prevent breaches.
Our solution supports a range of data protection laws, ensuring compliance with GDPR, CCPA, OIOO, and more.
Enforcing policies like Segregation of Duties (SOD) ensures no unauthorized access, preventing breaches and ensuring strong governance.

Connect effortlessly to 200+ endpoints across enterprise and cloud.









































































































Our platform is meticulously designed to provide a seamless integration experience, ensuring your data flows effortlessly across a diverse array of applications. Experience the unparalleled ease of connecting with over 200 applications effortlessly.










































































































ChainSys's solutions increase data discovery efficiency by 75%, enabling quicker access to relevant data assets and reducing the time spent on manual searches.
With ChainSys's pre-built connectors and templates, businesses can implement active metadata management solutions 50% faster than traditional methods.
ChainSys has successfully secured 5,000+ databases and millions of sensitive files globally.
ChainSys's solutions increase data discovery efficiency by 75%, enabling quicker access to relevant data assets and reducing the time spent on manual searches.
ChainSys's solutions increase data discovery efficiency by 75%, enabling quicker access to relevant data assets and reducing the time spent on manual searches.
Our solutions deliver 60%-80% cost and time savings, with built-in Pay-as-you-use pricing models.
ChainSys's solutions increase data discovery efficiency by 75%, enabling quicker access to relevant data assets and reducing the time spent on manual searches.
With ChainSys's pre-built connectors and templates, businesses can implement active metadata management solutions 50% faster than traditional methods.
The solution offers 3,000+ Smart Data Templates for data extraction, cleansing, and loading, reducing project time by over 60%.
ChainSys's solutions increase data discovery efficiency by 75%, enabling quicker access to relevant data assets and reducing the time spent on manual searches.
With ChainSys's pre-built connectors and templates, businesses can implement active metadata management solutions 50% faster than traditional methods.
ChainSys has facilitated GDPR, CCPA, etc, compliance for major enterprises, with clients achieving global implementation of PII identification in less than 6 months.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat.
